
Atlassian has announced that cyber criminals have been exploiting a vulnerability in its Confluence documentation system. Learn the cyber security risks and what you can do to protect your organization.
An Atlassian Confluence zero-day vulnerability has been reported as a common vulnerability and exposure (CVE) for users of the documentation system. Microsoft later discovered that the vulnerability was exploited by a nation-state threat actor for two weeks before Atlassian released a patch.
The US government has therefore warned international enterprise to protect themselves by updating to the latest version of Confluence as soon as possible. We, however, see this as another sign that organizations need to prioritize application modernization to prevent such threats before they happen.
To find out about which application modernization approach is right for you, download the latest Gartner® report. In the meantime, let's explore what the Atlassian Confluence vulnerability is and how you can protect your organization.
GARTNER® REPORT: How to Choose the Right Approach for Application Modernization and Cloud Migration
What Is Atlassian Confluence?
Confluence is a server or web-based, java-coded 'corporate wiki' created by Atlassian. The Australian company is known for its agile development management platform, Jira, but Confluence is an ancillary program intended to support software documentation.
Confluence is designed to store crucial information on software composition and processes. Not to mention, a key benefit is enabling collaboration and interconnectivity with other platforms, such as Jira.
This means a breach in the security of Confluence gives cyber criminals access to confidential information, process documentation that can expose further vulnerabilities, and routes to access other systems. This is why the security of Confluence is vital for the more than 13,000 companies that use it, as well as the US government.
What Is The Atlassian Confluence Vulnerability?
On September 14, 2023, a Chinese state-sponsored threat actor known as Storm-0062, DarkShadow, or Oro0lxy began exploiting a zero-day vulnerability in Atlassian Confluence, according to Microsoft. The group changed the US government's Confluence server’s configuration to indicate the setup was not complete and then used the "/setup/setupadministrator.action" endpoint to create a new administrator account.
This zero-day vulnerability allowed the threat actor group to read and edit the US government's software documentation for more than two weeks. Atlassian was swift to act once the vulnerability was discovered and offered a patch to remediate the vulnerability, but the patch only prevents further attacks and cannot remove the compromised admin accounts or undo their actions.
This represents a crucial danger to the US government, and the "handful of customers" Atlassian admits were also impacted by the vulnerability. The vulnerability is particularly challenging as it is a so-called 'zero-day' vulnerability.
What Is A Zero-Day Vulnerability?
A zero-day vulnerability like the one in Atlassian Confluence is one that has existed in the software since it was released, without the vendor knowing. This means the provider of the software has no lead time to find a way to mitigate the vulnerability - zero days.
Usually, the first to discover a zero-day vulnerability is the cyber criminal who exploits it. This is why zero-day vulnerabilities are the most pressing security issues to resolve.
It's hard to imagine a more-pressing zero-day vulnerability than one that has impacted the US government, but what does this mean for you? Should you be concerned for your business about the Atlassian Confluence vulnerability?
Should Confluence Customers Worry?
How big a concern the Atlassian Confluence vulnerability is for Atlassian customers is dependent upon their circumstances. Those that upgrade to version 8.3.4 or later before an illicit administration account is created will be safe from the vulnerability.
However, those Atlassian customers that may already have been compromised, whether they know it or not, will need to manually audit their admin accounts to find and remove any unauthorized administrator's access. This will be a daunting task, but thankfully, the vulnerability is currently only impacting those using the on-premise version of Confluence with an internet connection.
Those using the cloud-based version of Confluence will not be impacted by the vulnerability. We see this as a validation of cloud security.
Contrary to popular wisdom that cloud-native systems are a risk to security, modern, cloud-based applications are often less vulnerable to cyber attack than legacy systems. Whether you choose to migrate your IT landscape to the cloud or not, an application modernization effort is the best way to protect against zero-day software vulnerabilities.
Should You Move To The Cloud?
While cloud-based applications are less vulnerable to zero-day vulnerabilities like the Atlassian Confluence issue, that doesn't necessarily make cloud the right choice for your organization. Either way, older applications weren't designed to defend themselves against the complexity of modern cyber attacks.
Undergoing an application modernization initiative will assess whether moving fully or partly to the cloud is best for you. It will also ensure your application portfolio is as protected against cyber attack as possible.
However, completing an application modernization effort manually from scratch can be as challenging as auditing your Confluence accounts. That's why you need an application modernization platform that can automate the process and make it repeatable.
LeanIX EAM For Application Modernization
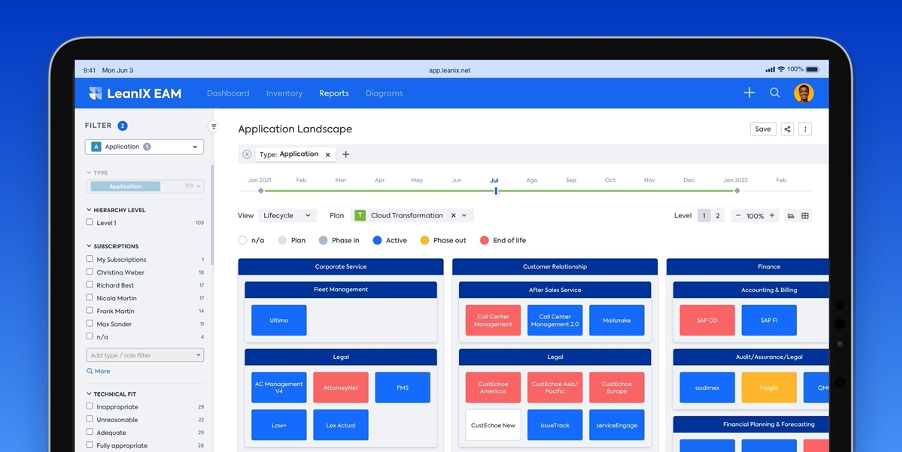
LeanIX EAM uses advanced user survey capabilities to catalog varied intelligence regarding each application in your portfolio. You can then use our platform to assess and categorize each application based on its security and cloud readiness.
Within LeanIX EAM, you can build a complete picture of your application portfolio and a roadmap for application modernization. All this information will then be preserved so modernization and software vulnerability remediation can become an ongoing process.
To find out more about how LeanIX EAM can enable application modernization and protect your organization from cyber attack, book a demo:



