
Technology supports and enhances almost every move we make as humans. From intricate banking procedures to shopping for groceries - every activity that we have embarked upon has been greatly influenced by technology. As the world becomes more interconnected, we also become more susceptible to risks. Just last week, one of the largest cyber attacks was announced, exposing the personal data of over 44% of the American population.
According to the 2017 Internet Security Threat Report, more than 7.1 Billion identities have been exposed in data breaches in the last 8 years. The average number of web attacks blocked per day is 229 thousand.
The potential magnitude of consequences from a technology hack are tremendous - organizations face legal liabilities, penalties, and damages to their public facing reputation.The monetary consequences are equally as detrimental. Investors typically sell shares on the heels of cyber attacks, which results in a more than a 5% dip in the stock prices of the companies affected.
As technologies are involved in the operation of many companies, organizations must put a sharp focus on managing technology risk.
How to Manage Risk?
On average, organizations use 928 cloud apps to support their business endeavors. Many businesses do not have a firm view of their application landscape, which can lead to high risks. Running unsupported versions of applications, the intricate and costly infrastructure supporting defunct legacy applications, and overpaying in license costs are major warnings that your organization does not have the full picture of your IT landscape.
4 Steps Technology Risk Management
- From life cycle to business impact, establish a standardized technology product information basis that includes current life cycle information from all of the applications and systems in place.
Tip: Use an EAM dashboard to gather the full picture of your IT Landscape.
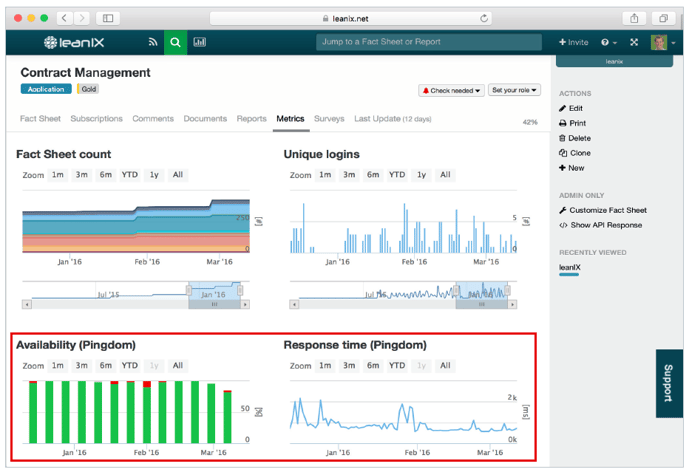 Figure 1 - LeanIX Metrics showing time-series data on availability and response time for one application.
Figure 1 - LeanIX Metrics showing time-series data on availability and response time for one application.
Successful technology risk management is data driven. Quantitative information displayed on the above enterprise architecture management platform will help you manage the risk of technology obsolescence.
- Analyze the potential business impact of each application. While the foundation of your technology risk management should be based on “hard” data, it is common practice and used to complete the picture with expert opinions from the applications main users. Main users can rate the technical fit of applications on a four-star scale based on easy to understand definitions. Does the application need technical upgrades to ensure ongoing support of business requirements?Is it adequate, with just some parts to be improved?
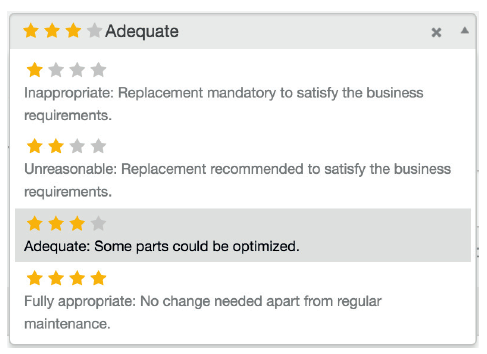
Figure 2 - LeanIX Application FactSheet - assessment of technical fit
The severity of the risk can be assessed by many different parameters: How many users are affected by a potential outage? What revenue impact does an application outage have? What are regulatory or compliance impacts? Does the technology risk result in an inability to meet needs for further business growth?
- Use a risk dependency map to easily visualize how many intricate dependencies are tied to one application.
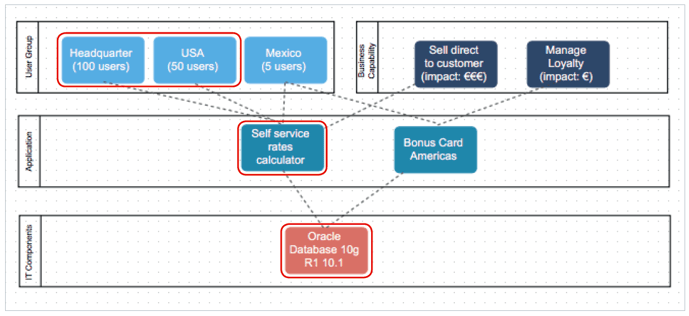
Figure 3 - LeanIX Visualizer showing a risk dependency map
- Place risk management high on the priority list.
As digital transformation rapidly quickens the pace of business expectations, it is easy for enterprise architects to focus the bulk of their attention on organizing their teams to deploy new code or deliver completed products to their stakeholders. These objectives are obviously important and will keep the organization competitive, but it is also equally imperative to have a strong focus on continual risk management.
Recent events have shown how the failures in technology can cause lasting damage to the reputation of organizations. Put these steps in place to effectively manage technology risk in the digital age.




